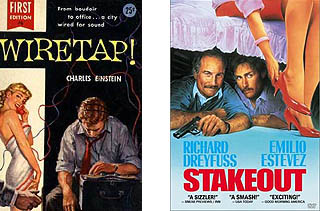
I honestly don’t know which is worse.
(also check out Part 1 and Part 2)
The press and Bush’s supporters make a big deal out of the fact that the NSA’s phone records program does not actually involve wiretaps. I think that’s a red herring.
My argument is that the program is effectively a massive stakeout of every single American citizen. It’s the electronic equivalent of stationing a federal agent outside of every one of our homes, and having them follow us around all day, writing down every person we talk to, every business we interact with, and (in theory) everything we buy, everywhere we travel, and potentially much more.
So even if it’s not a wiretap, it’s still spying. Domestic spying. On you and me.
It is NOT anonymous
Many articles on the subject say the NSA’s records are “anonymous”. The Washington Post’s Richard A. Falkenrath says as much in an editorial on the WaPo’s increasingly Bush-friendly editorial page:
The Telecommunications Act of 1934, as amended, generally prohibits the release of “individually identifiable customer proprietary network information” except under force of law or with the approval of the customer. But, according to USA Today, the telephone records voluntarily provided to the NSA had been anonymized.
This is a lie, of course. Nothing has been “anonymized”. Anybody who has a person’s phone number can get access to their name in a heartbeat, especially the NSA. Unless you’re the kind of person who also thinks that saying “the wife of Joseph Wilson is a CIA spy” isn not effectively the same thing as saying “Valerie Plame is a CIA spy”.
Almost any peice of seemingly anonymous information about a person can, even by a child with access to Google, be linked to that person’s name, address, and much, much more.
The NSA’s database is not anonymous. Every phone number is (not “can be” but “is“) individually identifyable. If you only understand one thing I say about this program, it should be this: The government knows every single person, company, or organization you’ve called, by name, for the last 4+ years.
For far more debunking like this and more information on how the NSA’s data can be used non-anonymously, read this excellent article by Mash at docstrangelove.com.
It is NOT just guilty people
As I’ve noted before, they’re almost certainly building/modeling our social networks to define who we know and who we are connected to. Part of the problem, however, is explaining the idea of “networks” to people. USA Today tried to explain the technology:
The NSA puts the ever-growing database through what it calls “traffic analysis” to discern patterns of phone calling using powerful computer programs, the officials said.
The NSA’s analysis sometimes starts with a specific telephone number and then examines all calls to and from that number. From there, the former intelligence official said, “You build a big spider web moving outward, looking at the calls to the original number, then the calls to and from those numbers and so on.”
I don’t know about you, but this doesn’t paint a very clear picture to me. It’s like saying that they have a “tachyon beam” or something. It doesn’t explain what this means, just what it is.
Again, the press needs to think these issues through more. They need to interview people who can imagine how far this program could go, because with database mining it’s pretty much a given that anything that can be done will be done.
It’s NOT just the phone records
NSA computer scientists can use this data to reconstruct eerily complete profiles of every one of us. They can build incredibly detailed dossiers on each of us simply by “mashing up” different databases. A poster named “James” at ThinkProgress had this observation:
On another note, you CANNOT form CONCLUSIONS about telephone records without OTHER DATABASES. Relational statistics REQUIRES something to compare that to or the results would be meaningless (look at SAS or SPSS’s software for example which is used for datamining and they both have classified contracts). You MUST have things like BUYING HABITS, TRAVEL HABITS, etc to make ’sense’ of this stuff.
It’s likely the NSA is buying more than just telephone records – it’s likely they’re buying credit reports, etc to be able to perform relationships. Otherwise the program would be senseless.
If people realized that their telephone records were being compared to their transaction records I think there would be more of an outcry.
Let’s add a few more items to this potential database-cross-referencing scheme:
- Your online profiles and social networks (MySpace, Friendster, Flickr, etc)
- Your posts and comments online
- Your medical records
- Your employment records
- Your EZ-Pass/QuickPass records, and other electronic mass-transit records
Honestly, I think we need a privacy amendment to the Constitution.
This stuff will never go away
Computer records are almost never, ever destroyed. They linger around forever and ever. If you’ve ever tried to fix an error on your credit report or remove yourself from a mailing list, you know what I mean.
Even when this War on Terror ends (ha), don’t count on the goveovernment destroying these records. More likely they will find a way to hold on to them forever. At best they will just lose track of them, and they will eventually leak into the hands of other government agencies, private companies, or to the general public.
There are plenty of good reasons why Congress has passed many laws to prevent the government from ever doing this.
Bush is turning normal Americans into spies
They’re building secret rooms across the country, and recruiting hapless telecom workers to help the NSA spy on us:
According to a statement released by Klein’s attorney, an NSA agent showed up at the San Francisco switching center in 2002 to interview a management-level technician for a special job. In January 2003, Klein observed a new room being built adjacent to the room housing AT&T’s #4ESS switching equipment, which is responsible for routing long distance and international calls.
“I learned that the person whom the NSA interviewed for the secret job was the person working to install equipment in this room,” Klein wrote. “The regular technician work force was not allowed in the room.”
Klein’s job eventually included connecting internet circuits to a splitting cabinet that led to the secret room. During the course of that work, he learned from a co-worker that similar cabinets were being installed in other cities, including Seattle, San Jose, Los Angeles and San Diego.
I want to give props to WIRED magazine, by the way, for their excellent coverage of this issue so far. They gave Clinton/Gore such a hard time over Echelon, I should hope that they give the Bushies ten times as much scrutiny and criticism now that it’s all come true.
Go to “NSA Data Mining 1: If you aren’t against it, then you don’t really understand it.”
Go to “NSA Data Mining 2: So you think you have nothing to hide?”
Comments
3 responses to “NSA Data Mining 3: Wiretaps? Maybe not. Stakeouts? Definitely.”
I agree completely about the absurdity of claiming the data is anonymous, as well as about the potential for abuse within this system. I’ve written about it at some length here:
http://www.sindark.com/2006/05/16/government-and-secrecy/
Thanks, Milan. I checked your blog, and you say what I’m about to say in Part 4 (the final part) of this series: That the secrecy, lack of oversight, and the apparent illegality of the programs are the worst parts of this whole ugly thing.
Christopher,
If you don’t already read it, I recommend the following security related blog:
http://www.schneier.com/blog/
You may well find it interesting.